-
SnapOS
-
-
- Articles coming soon
-
-
-
- Citrix HDX + USB Headset (Call-Center Baseline)
- OS/Firmware Update & Rollback
- Power Management and Session State
- Wi-Fi Roaming & Link Change Mid-Session
- Kiosk / Assigned-Access Auto-Launch
- Barcode Scanner (HID) with Line-of-Business App
- Printing to Local USB & Network Printers
- USB Device Management – Block Storage
- Multi-Monitor & 4K Performance
- Microsoft AVD/RDP + Teams Optimized Video
- VMware Horizon + Smart Card / CAC Login
-
-
-
-
zWAN
-
-
-
-
- Firewall & Layer 7 Application Filtering
- VPN Site-to-Site Tunnel Setup & Connectivity (z40 to Cloud vGR)
- Intrusion Prevention System (IPS) / Intrusion Detection System (IDS) Testing
- DNS Filtering
- DDoS Protection & Logging
- MAC Address Filtering & Geo-fencing
- Application Control & Protocol Blocking
- Authentication & Access Control (zID)
-
- WAN Link Failover & Load Balancing (ACI Mode)
- Dynamic Path Selection & Application-Aware Routing
- SaaS & Internet Breakout Validation
- QoS for Microsoft Teams (Datacenter vGR + Branch z40)
- Tunnel Failover (z40 ↔ vGR) — WAN00 (wired) primary, WAN03 (4G) & WAN04 (5G) backups
- IP Routing & Static Route Steering (z40 Branch)
- VLAN & Layer-2 Bridging
-
-
-
-
-
-
- Articles coming soon
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
- Articles coming soon
-
- IPsec Tunnel not Establishing
- SSL-VPN Tunnel not Establishing
- Mobile Network Issues
- Management Tunnel does not Establish
- DNS not Resolving from Local Network Appliance
- DNS Resolution Issues in Tunnel Configuration
- DHCP Server not Leasing IP to LAN PC
- Debugging EC Events - Unknown Status Issue
- Trusted-MAC Geofencing Issues
- DNS Issues from DC LAN PC
- Troubleshooting LAN Connectivity to Internet via WAN, Remote Branch LAN, or Local Branch LAN
- NetBalancer gateways displaying Faulty/Inactive
- Packet Drop Issues
-
-
zAccess
-
StorTrends
DHCP IPV4
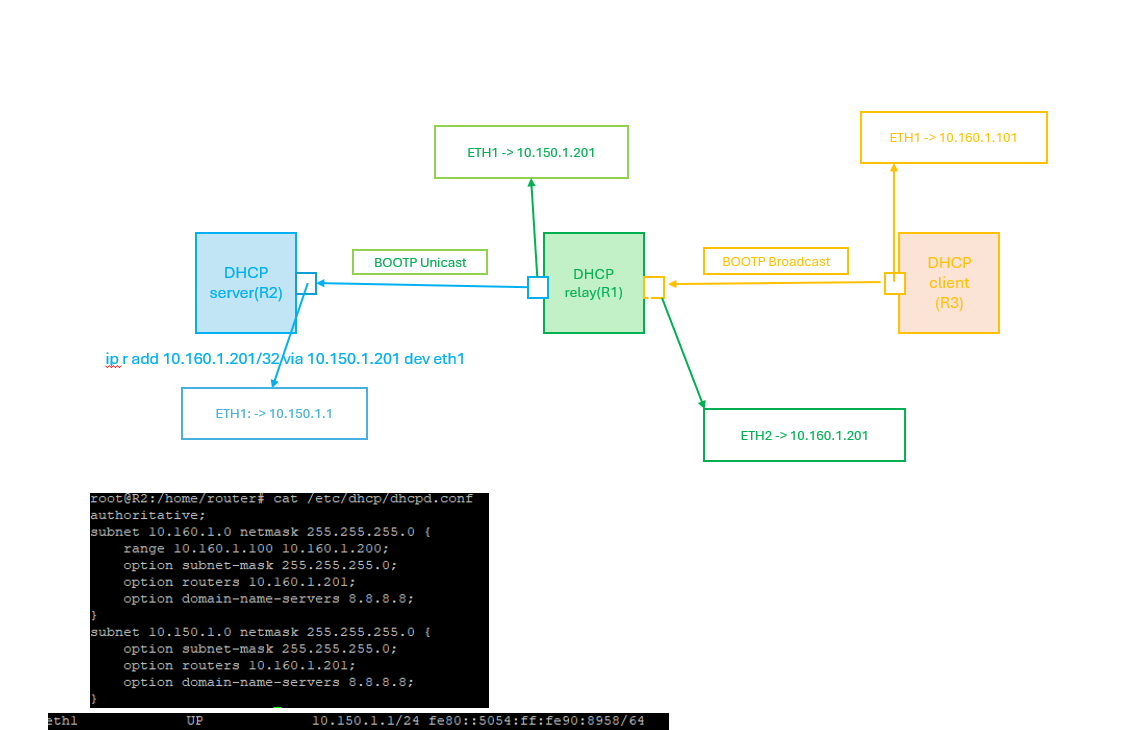
DHCP relay agent provides a method of relaying/forwarding DHCP and BOOTP requests from a DHCP client and DHCP server on different IP networks. It acts as an interface between DHCP client and the server. The DHCP Relay Agent listens for DHCPv4 or DHCPv6 queries from clients or other relay agents on one or more interfaces, passing them along to upstream servers . When a reply is received from upstream, it is multicast or unicast back downstream to the source of the original request. This page explains about configuring DHCP Relay in zWAN CPE for IPV4.
The DHCP relay service allows you to pass DHCP broadcast messages to network segments that a client computer is not directly attached to. DHCP relaying can be used to share a single DHCP server across logical network segments that are separated by a firewall. The DHCP relay service does not handle IP addresses. It sends unicast messages instead of broadcast messages.
A sample DHCP Relay network topology is depicted below.
Pre-requisite:
- DHCP server config should be disabled/deleted on interfaces which is to be added part of DHCP relay configuration.
Functionality
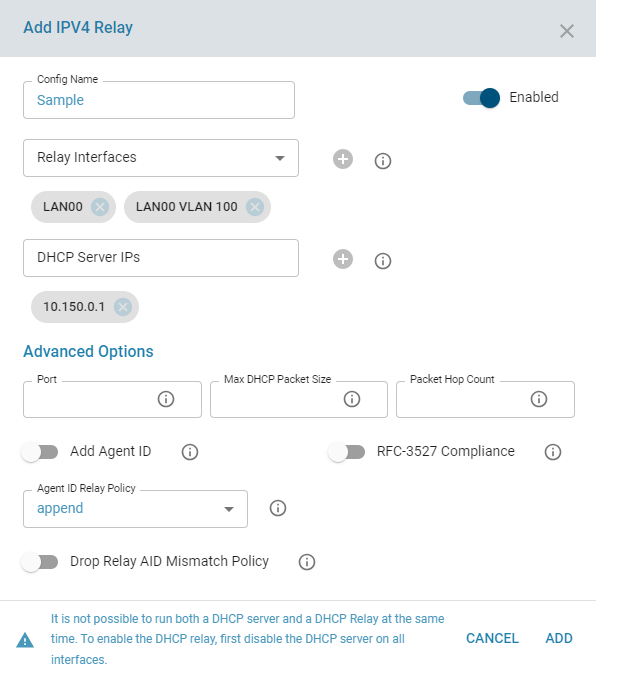
The zWAN CPE can be configured for DHCP relay by adding the DHCP server IP and the relay interfaces in the zWAN CPE.
Parameters
- Config Name: Configuration Name for reference
- Config Status : Configuration Status to enable the specifc relay server config
- Server IP : IP addresses of the DHCP server
- Relay interfaces : Network interfaces that are used by the DHCP relay agent to connect to the DHCP server and client networks. Add incoming (connected to the client network) and forwarding (connected to DHCP server) interfaces . Minimum 2 interfaces is required.
Advanced Options
- Port : Listen and transmit on port PORT. This is mostly useful for debugging purposes. Default is 67
- Max Packet Size : Specify the maximum packet size in bytes to send to a DHCPv4/BOOTP server. This might be done to allow sufficient space for addition of relay agent options while still fitting into the Ethernet MTU size. Default 1400 Bytes
- Add AgentID : Append an Agent ID field to each request from relay server before forwarding to the DHCP server. An agent ID indicates that the data has been relayed.Agent option fields in responses sent from servers to clients will be stripped before forwarding such responses back to the client
. - Relay AIDPolicy: Control the handling of incoming DHCPv4 packets which already contain relay agent options. If such a packet does not have giaddr set in its header, the DHCP standard requires that the packet be discarded. However, if giaddr is set, the relay agent may handle the situation in four ways: It may append its own set of relay options to the packet, leaving the supplied option field intact; it may replace the existing agent option field; it may forward the packet unchanged; or, it may discard it. Default is 'append'. Note: Using relay policy options such as replace or discard on relays upstream from one using RFC 3527 compliance can pose problems.
The relay agent will wipe out the initial relay agent option containing the link selection while leaving the re-purposed giaddr value in place, causing packets to go astray.. - Drop Reply AID Mismatch Policy: Drop packets from upstream servers if they contain Relay Agent Information options that indicate they were generated in response to a query that came via a different relay agent. If this option is not specified, such packets will be relayed anyway. The Reply AID Mismatch Policy setting is important when multiple relay agents serve the DHCP server.
- Packet HopCount: When forwarding packets, dhcrelay discards packets which have reached the configured hop count. Default is 10. Maximum is 255
t - RFC 3527 Complaince and Getway Inteface: Enables the addition of a RFC 3527 compliant link selection suboption for clients directly connected to the relay. This RFC 3527 option allows a relay agent to specify two different IP addresses: one for the server to use when communicating with the relay (giaddr) the other for choosing the subnet for the client (the suboption). This can be useful if the server is unable to send packets to the relay via the address used for the subnet. Note: Using relay policy options such as replace or discard on relays upstream from one using RFC 3527 compliance can pose problems. The upstream relay agent will wipe out the initial
relay agent option containing the link selection while leaving the re-purposed giaddr value in place, causing packets to go astray. This option is off by default.
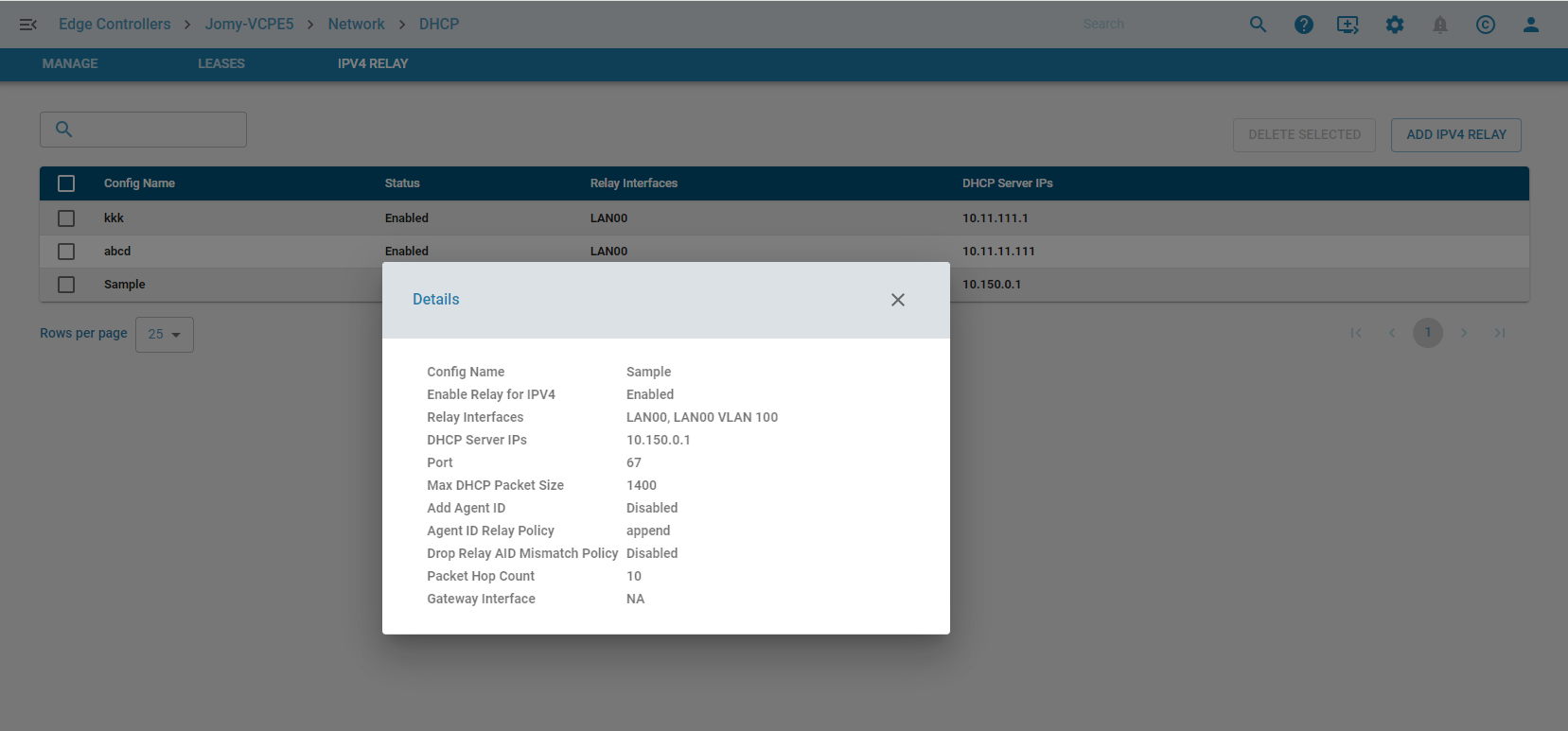
Functionalities in UI:
- Add V4 Relay configuration
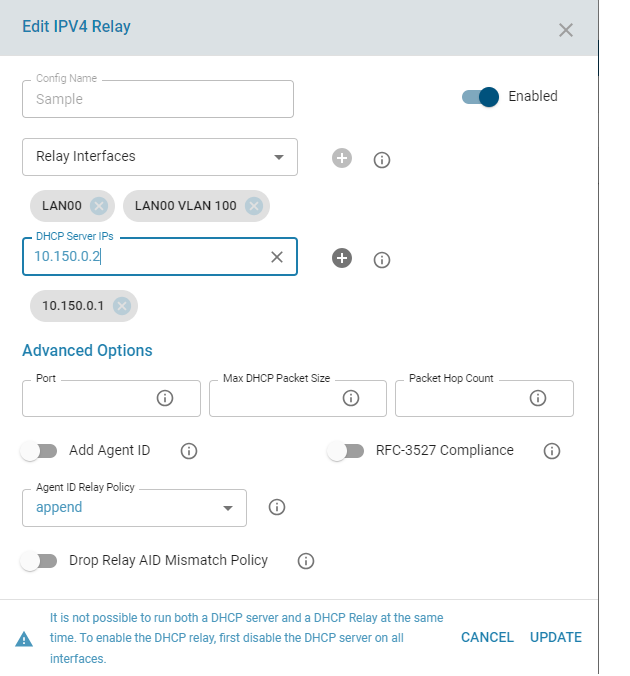
- Edit V4 Relay configuration
- Delete V4 Relay configuration
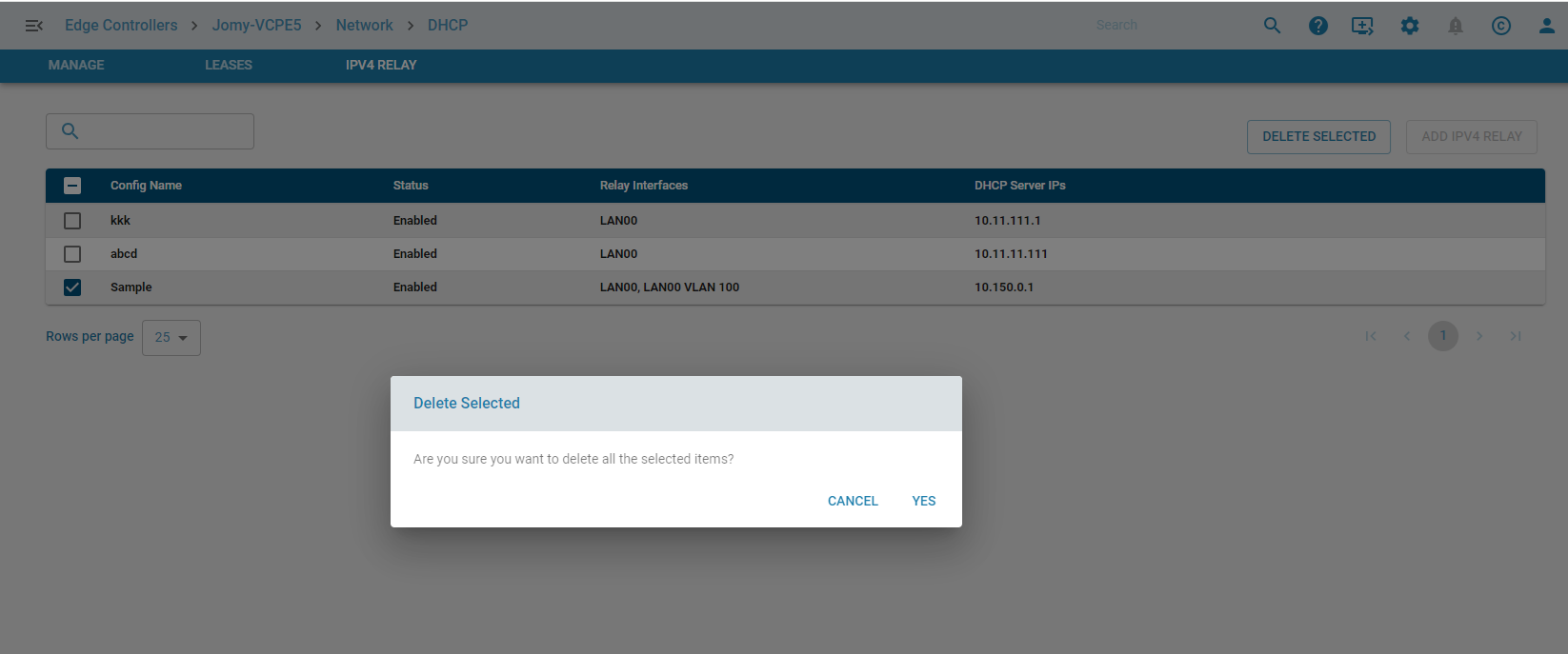
- List V4 Relay configuration
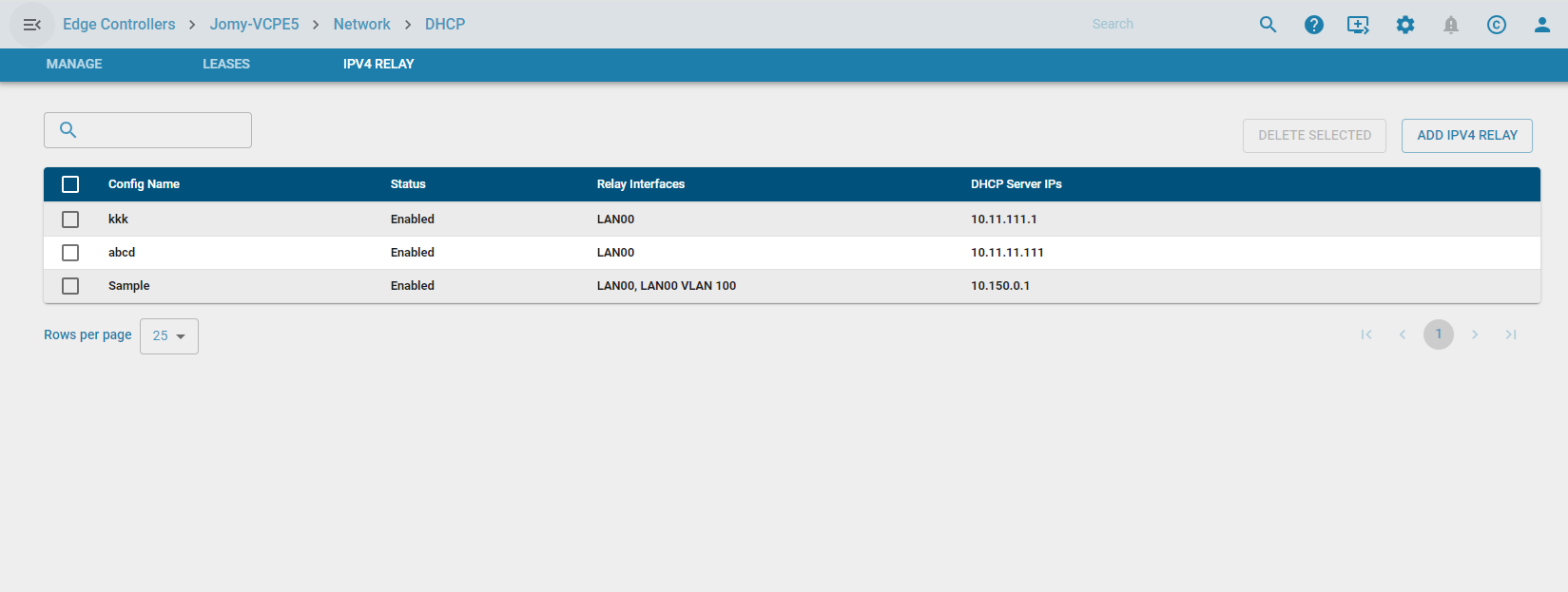
- Display Config Info