Authentication Control
The Authentication Management section is focused on configuring user authentication and application access through the gateway.
User Groups and Application Groups make it easier to administer access controls. It is much more efficient to create User Groups and Application Groups, and then specify privileges for entire groups instead of specifying for individual users or applications.
AUTHENTICATION DOMAIN
The Authentication Domain page in the management console allows the administrator to define the authentication and authorization scheme for zGateway, termed as Authentication domain. It is now possible to add multiple Authentication domains each with own AAA scheme.
AUTHENTICATION SERVERS
An administrator can add and use more than one external authentication server. A maximum of five Authentication Servers can be configured in cascading manner using the priority. This means, if user cannot be found in highest priority server, the user will be searched in the lower priority servers also.
To configure the zGateway Authentication priority, open the Management Console and expand Access Management. Select VPN Domain from the submenu.
Simply use the drop down list in the Authentication Servers box to specify the priority order for authenticating users to zGateway.
You can delete servers from the priority list by using the Delete Server option.
NB: Deleting servers from this list does NOT remove the authentication servers from the system.
AUTHORIZATION SERVERS
In case the authentication server cannot provide role/group information for an incoming user, a separate authorization server can be specified which will be used to provide user role information. Authentication servers like OTP tokens or RSA Secure ID servers may not provide role information to zGateway. zGateway requires user’s role to assign applications to the user. With such servers an additional external authentication server or native groups can be used to decide the role of the user. The authentication is done with the external authentication server and then the username is searched in the configured external authorization server.
Authorization servers can also be configured in cascading manner using the priority. A maximum of two authorization servers can be configured. Selecting the option same as Authentication Server will cause the authorization to happen with the authentication server through which the user is authenticated.
Simply add your chosen Authentication server which is to be used for Authorization search on login.
AUTHENTICATION SERVERS
As well as having a local database of users who can authenticate to zGateway, you can configure authentication servers which will allow integration with LDAP based directories such as Active Directory or RADIUS based authentication systems. Once configured, these Authentication Servers become active in the VPN Domains and Access Controls pages.
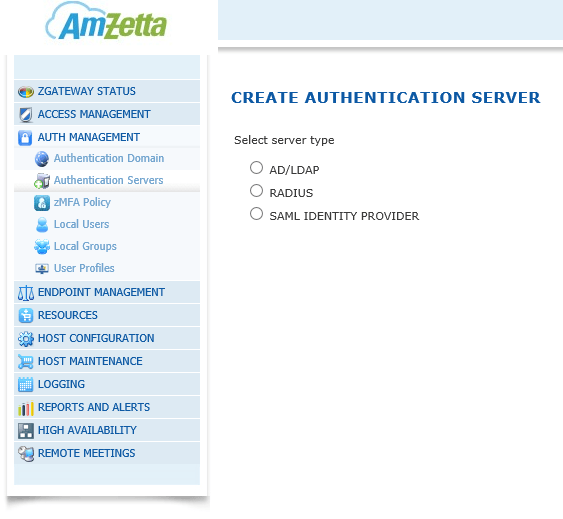
ADD AUTHENTICATION SERVER
Open zGateway management console, click to expand Access Management, and then click Authentication Servers. Click Add to specify a new Authentication Server. Choose from one of AD/LDAP, Radius or zMFA
AD/LDAP AUTHENTICATION SERVER
Type an identifier of the External AD/LDAP Authentication Server in Server Name field.
Type the IP address, host name, or FQDN of the AD/LDAP server, in the Host Name field.
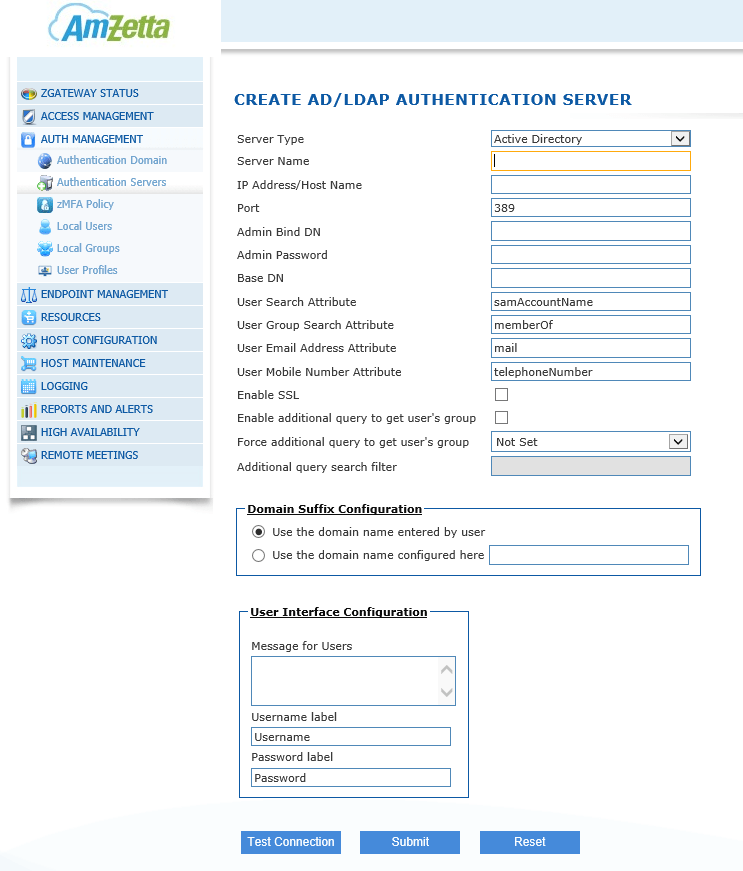
The default LDAP port number is displayed in the Port field. Please note that you can change this port number as needed.
Type the admin bind DN in the Admin Bind DN field e.g. cn=vpnadmin,cn=Users,dc=prodemo,dc=local
Type your password in the Admin Password field.
Type the base DN in the Base DN field e.g. dc=prodemo,dc=local
User search attribute is given in the User Search Attribute field, e.g. samAccountName.
User Group search attribute for the server is displayed in User Group Search Attribute field, e.g. MemberOf.
NB: The User Group Search Attribute is used to obtain the User Groups from AD/LDAP server.
Click Test Connection to verify the configuration. If this is successful then click Submit to save the configuration data or Reset to clear all data from this screen.
AD/LDAP Configuration info updated successfully message will be displayed.
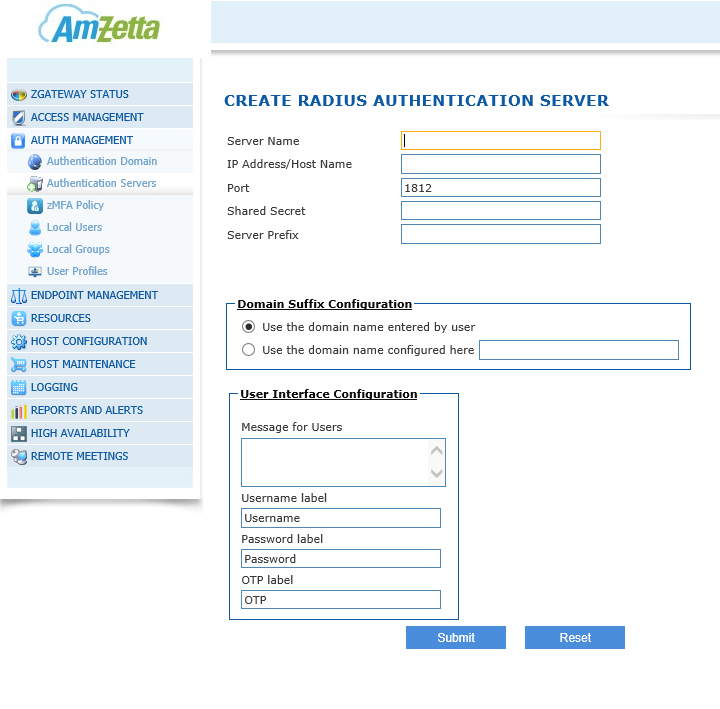
RADIUS AUTHENTICATION SERVER
Type an identifier of the External RADIUS Authentication Server in Server Name field.
Type the host name, or FQDN of the RADIUS server, in the Host Name field.
The default RADIUS port number (1812) is displayed in the Port field. Please note that you can change this port number as needed.
Type the administration password of the RADIUS server in the Shared Secret field.
Click Submit to save the configuration data or Reset to clear all data in this screen. Radius configuration info updated successfully message will be displayed.
NB: The AD/LDAP and RADIUS users must download the root certificate (cacert.cer) and import it to the list of Trusted Root Certification Authorities.
zMFA
zMFA is a two factor authentication solution that provides One Time Passwords delivered via multiple mechanisms including hard tokens, soft tokens, email, SMS, PKI tokens and web tokens. zGateway can authenticate user’s with zMFA server by calling its authentication API running over HTTPS rather than using plain text UDP based RADIUS protocol.
One or more zMFA servers can be created and assigned to VPN domain. zMFA server only provides authentication services. Authorization service is not provided by zMFA server. We recommend Active Directory is used in conjunction with zMFA to provide group assignment of resource access.
For more information on installing and configuring the zMFA server please refer to zGateway – zMFA Install Guide.
Type an identifier of the External zMFA Authentication Server in Server Name field.
Type the IP address, host name, or FQDN of the zMFA server, in the Host Name field.
The port number should be changed to 8443 in the Port field.
Type the Organization ID on the zMFA authentication server in the Org ID field. (Contact your zMFA Authentication Server administrator to get the Org ID value).
Type the Caller ID on the zMFA authentication server in the Caller ID field. (Contact your zMFA Authentication Server administrator to get the Caller ID value).
The Tokens listed can be enabled and used to authenticate users.
Enable Dual Authentication – If checked user will be asked to enter zGateway credentials as well as OTP.
User Interface Configuration:
Message for users – This message will be sent to user with OTP
Username label, Password label, OTP labels – These labels will be displayed to the user in the portal.
Click Submit to save the configuration data or Reset to clear all data in this screen.