-
zWAN
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
-
-
zTC
-
StorTrends
-
zPortal
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
zGateway
-
Firewall
0 out Of 5 Stars
| 5 Stars | 0% | |
| 4 Stars | 0% | |
| 3 Stars | 0% | |
| 2 Stars | 0% | |
| 1 Stars | 0% |
Overview
zWAN offers a very rudimentary firewall for basic packet filtering. This is done using Netfilter and iptables. Packets can be filtered based on rules/conditions set on the packet headers and their correlation with connections or already transited packets. The default chains INPUT, FORWARD and OUTPUT are available. The ability to add custom or user defined chains which can be the target of the preset ones is also present.
Functionality
The flow classifier module is used to configure the firewall rules and determine whether to ACCEPT, DROP, REJECT, RETURN or Jump to a user define chain. Refer to the flow Classification module for how to set Rules. Rules can be added to the chains. System has three default (built-in) chains
- INPUT chain – packets designated to Edge Controller will be checked against INPUT chain
- FORWARD chain – packets routed through the Edge Controller will be checked against FORWARD chain
- OUTPUT chain – packets originated at Edge Controller will be checked against OUTPUT chain
- User can create Custom chain and add rules to it. Custom chain can be linked with the default Chain mentioned above.
Based on the filter, both incoming and outgoing packets are accepted or dropped. It can jump to a custom chain (which has further rules) before it is accepted or dropped.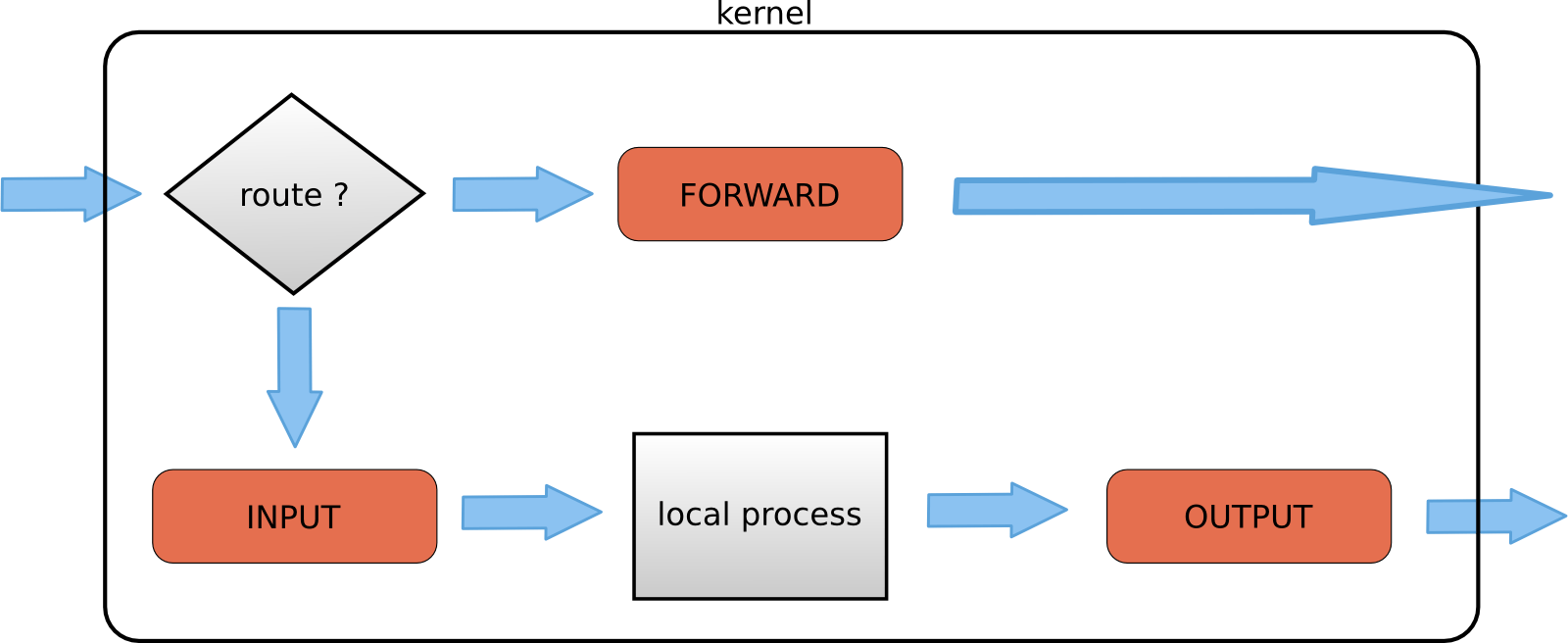
Add Chain

Add rule
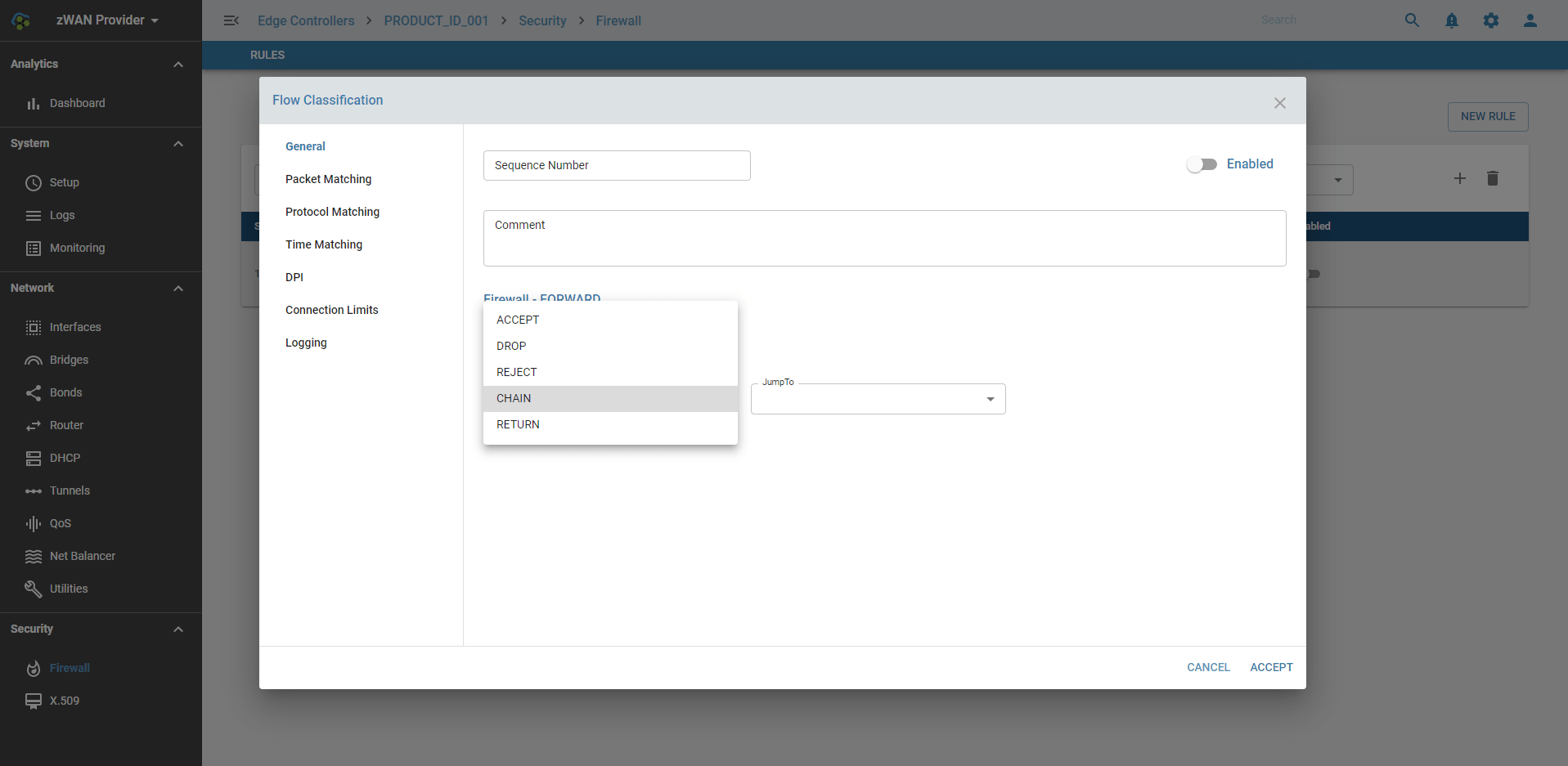
Default Policy
If no rule is set for that chain or no decision is made (since no matching rule for the packet in that chain), the sytem will take default policy for that chain, which is either ACCEPT or DROP. If the target is not set explicitly for a rule, the rule will take the default policy for that chain.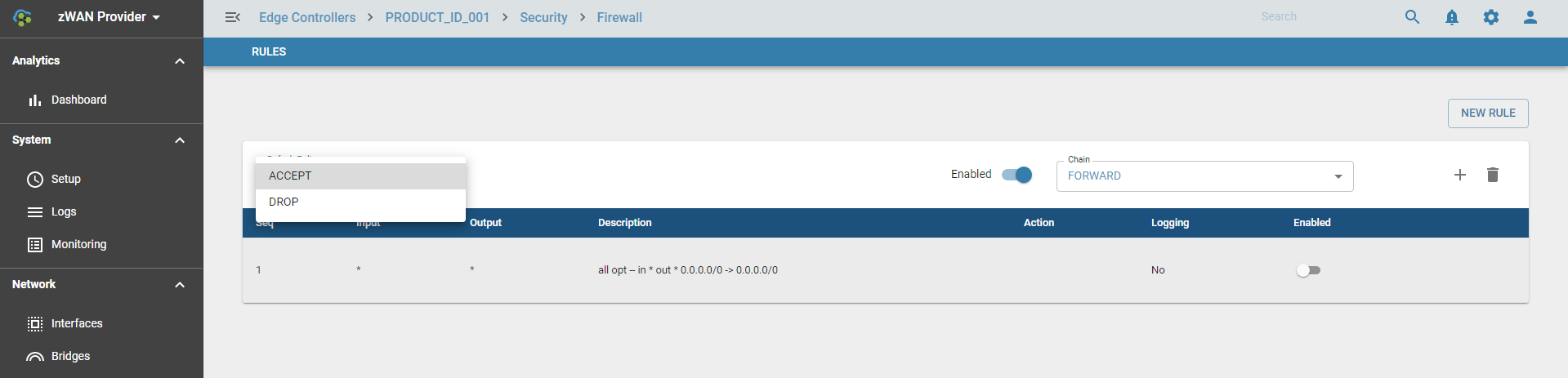
Firewall is designed to prevent unauthorized access to or from a Branch network.
Known Limitation
- Up to 999 Rules per Chain
0 out Of 5 Stars
| 5 Stars | 0% | |
| 4 Stars | 0% | |
| 3 Stars | 0% | |
| 2 Stars | 0% | |
| 1 Stars | 0% |