-
SnapOS
-
-
- Articles coming soon
-
-
-
- Citrix HDX + USB Headset (Call-Center Baseline)
- OS/Firmware Update & Rollback
- Power Management and Session State
- Wi-Fi Roaming & Link Change Mid-Session
- Kiosk / Assigned-Access Auto-Launch
- Barcode Scanner (HID) with Line-of-Business App
- Printing to Local USB & Network Printers
- USB Device Management – Block Storage
- Multi-Monitor & 4K Performance
- Microsoft AVD/RDP + Teams Optimized Video
- VMware Horizon + Smart Card / CAC Login
-
-
-
-
zWAN
-
-
-
-
- Firewall & Layer 7 Application Filtering
- VPN Site-to-Site Tunnel Setup & Connectivity (z40 to Cloud vGR)
- Intrusion Prevention System (IPS) / Intrusion Detection System (IDS) Testing
- DNS Filtering
- DDoS Protection & Logging
- MAC Address Filtering & Geo-fencing
- Application Control & Protocol Blocking
- Authentication & Access Control (zID)
-
- WAN Link Failover & Load Balancing (ACI Mode)
- Dynamic Path Selection & Application-Aware Routing
- SaaS & Internet Breakout Validation
- QoS for Microsoft Teams (Datacenter vGR + Branch z40)
- Tunnel Failover (z40 ↔ vGR) — WAN00 (wired) primary, WAN03 (4G) & WAN04 (5G) backups
- IP Routing & Static Route Steering (z40 Branch)
- VLAN & Layer-2 Bridging
-
-
-
-
-
-
- Articles coming soon
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
- Articles coming soon
-
- IPsec Tunnel not Establishing
- SSL-VPN Tunnel not Establishing
- Mobile Network Issues
- Management Tunnel does not Establish
- DNS not Resolving from Local Network Appliance
- DNS Resolution Issues in Tunnel Configuration
- DHCP Server not Leasing IP to LAN PC
- Debugging EC Events - Unknown Status Issue
- Trusted-MAC Geofencing Issues
- DNS Issues from DC LAN PC
- Troubleshooting LAN Connectivity to Internet via WAN, Remote Branch LAN, or Local Branch LAN
- NetBalancer gateways displaying Faulty/Inactive
- Packet Drop Issues
-
-
zAccess
-
StorTrends
DDOS Configuration
Overview:
Distributed Denial of Service or more commonly known as DDoS attack is an malicious attempt to disrupt the normal flow of traffic of a targeted server, or network byt overwhelming the target with a flood of internet traffic.
zWAN provides basic support for DDoS or DoS attacks, but if the attacker's traffic has already passed your ISP and reaching the EC, the link to the EC is already exhausted which would disrupt the normal traffic flow. What zWAN DDoS does is that, once an attack is detected based on the thresholds configured, it will stop processing the packets and drop them. This prevents wastage of CPU and Memory resources on the EC and also prevents any KP or OOM killers from getting exercised.
Functionality:
- DDoS can be enabled/disabled on a global basis
- DDoS can be enabled/disabled on a per WAN interface
- Attack Thresholds can be set for different type of traffic per source. The attacks thresholds are mainly
- ICMP FLOOD Defaults : 300 packets/sec
- UDP FLOOD Defaults : 1000 packets/sec
- TCP SYN Defaults : 300 packets/sec
- TCP RST Defaults : 50 packets/sec
- SSH BRUTEFORCE Defaults : 10 packets/sec
- IPs that attempted to attack or portscan the EC can be viewed
- Permanent or temporary allowLists and blockLists are supported
Please note : In order for DDOS to work, the firewall INPUT policy should be set to default DROP.
Configuration Parameters
DDOS Status

Configure DDOS per interface
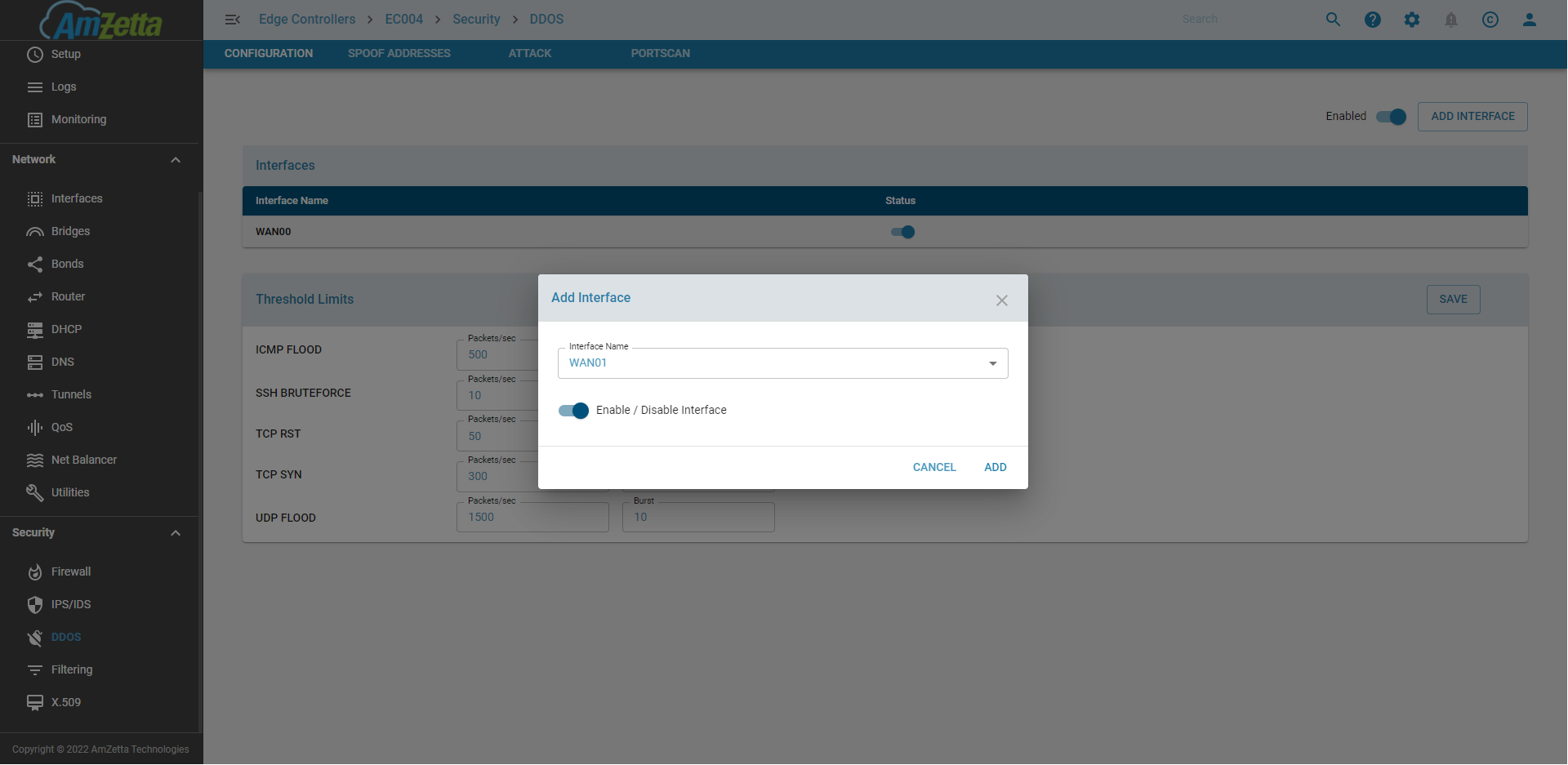
DDOS Settings for ICMP FLOOD, UDP FLOOD, TCP SYN, TCP RST, and SSH BRUTEFORCE

DDOS IP List
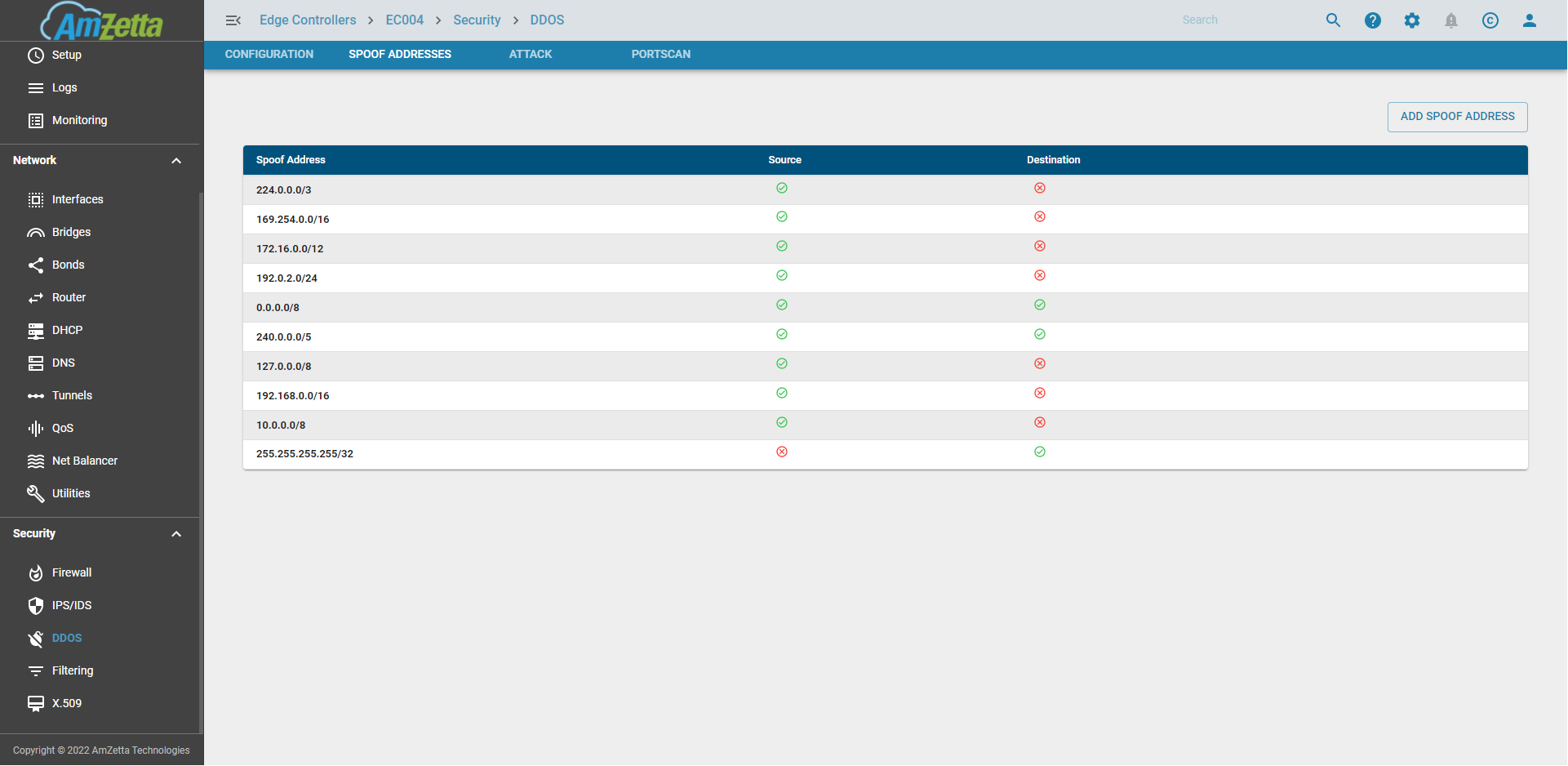
- Spoofed Addresses
There are IP Networks which are not seen if the EC is directly facing the Internet Network. If the EC is in an internal network and if a 10.0.0.0/8 ip is possible then the spoof address entries need to be updated accordingly before enabling DDOS
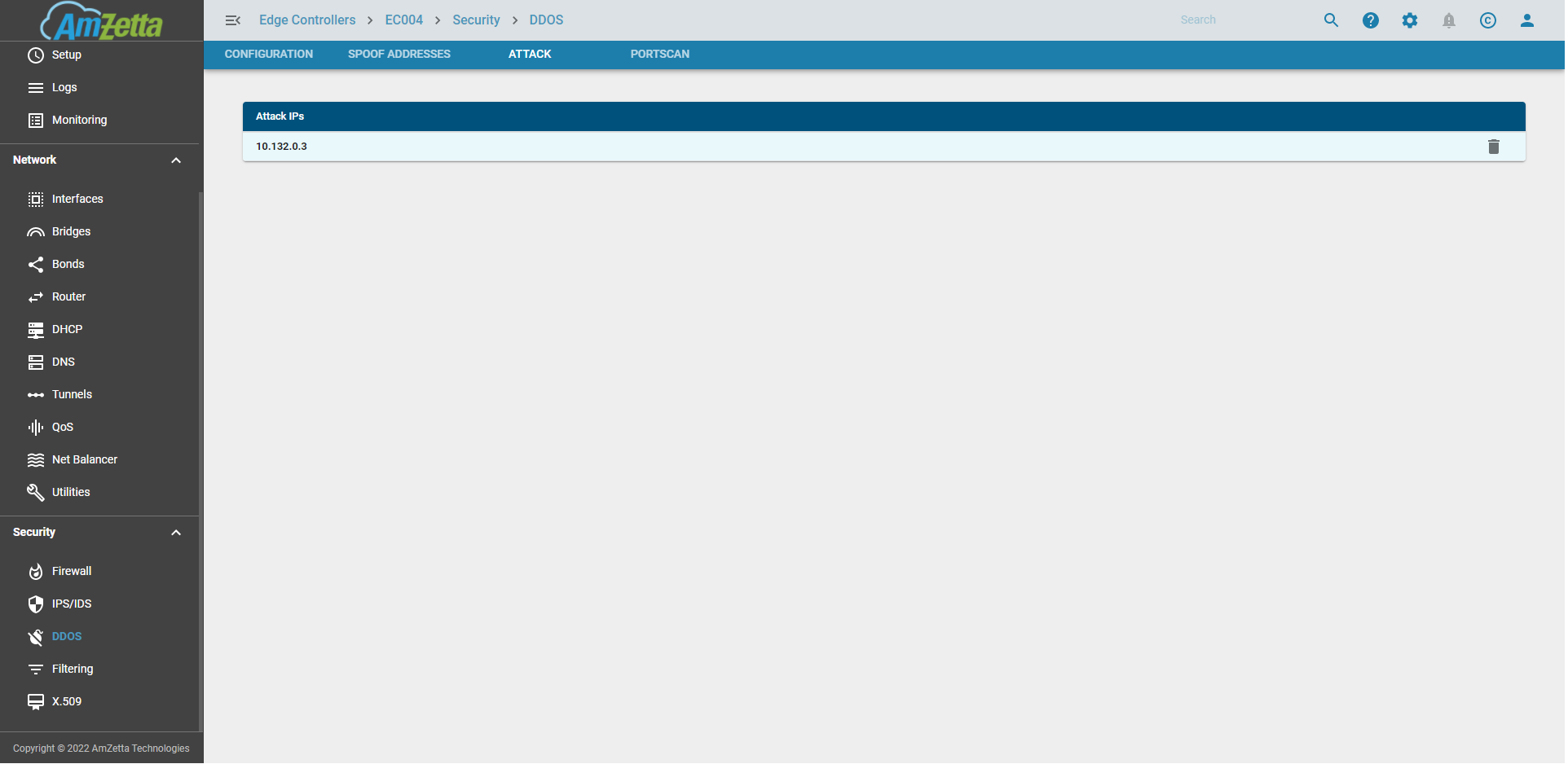
- Attack
IPs that attempted to attack or portscan the EC will be added to a temporary DDOS List for a 5 minute time period. The 5 minute timeperiod is enforced so that any false positives get automatically removed from the list after that time or even manually removed by the user.
Note : TCP-RST attacks will not be added to the DDOS list as they are spoofed IPs of actual source machines. If a TCP-RST attack is detected then we will drop the packets based on the threshold configured and log the same.
- PortScan
There are external devices which try to run a portscan on the EC. They are then blocked of for a day. If there is a false positive then those IPs can be manually removed by the user.
