-
SnapOS
-
-
- Articles coming soon
-
-
-
- Citrix HDX + USB Headset (Call-Center Baseline)
- OS/Firmware Update & Rollback
- Power Management and Session State
- Wi-Fi Roaming & Link Change Mid-Session
- Kiosk / Assigned-Access Auto-Launch
- Barcode Scanner (HID) with Line-of-Business App
- Printing to Local USB & Network Printers
- USB Device Management – Block Storage
- Multi-Monitor & 4K Performance
- Microsoft AVD/RDP + Teams Optimized Video
- VMware Horizon + Smart Card / CAC Login
-
-
-
-
zWAN
-
-
-
-
- Firewall & Layer 7 Application Filtering
- VPN Site-to-Site Tunnel Setup & Connectivity (z40 to Cloud vGR)
- Intrusion Prevention System (IPS) / Intrusion Detection System (IDS) Testing
- DNS Filtering
- DDoS Protection & Logging
- MAC Address Filtering & Geo-fencing
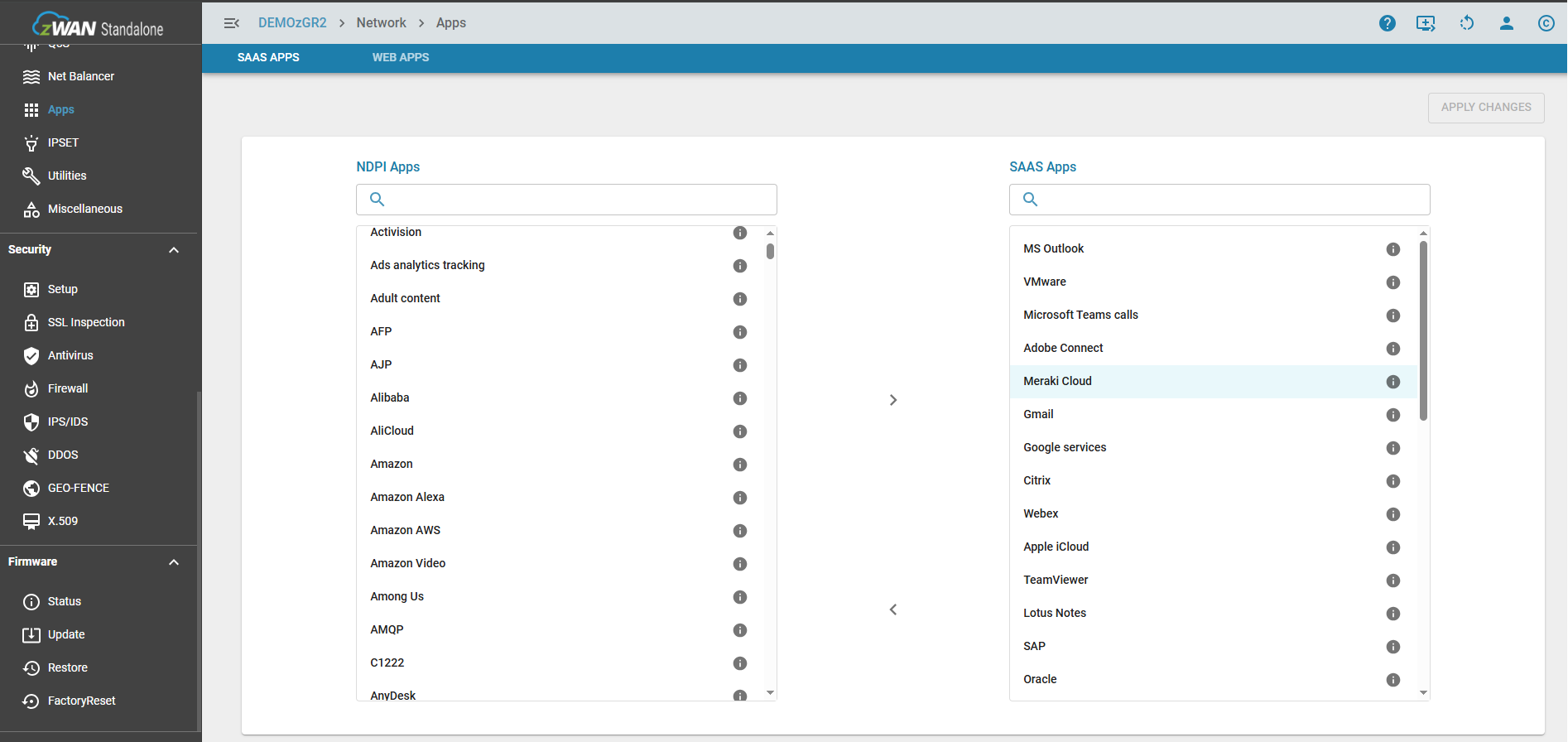
- Application Control & Protocol Blocking
- Authentication & Access Control (zID)
-
- WAN Link Failover & Load Balancing (ACI Mode)
- Dynamic Path Selection & Application-Aware Routing
- SaaS & Internet Breakout Validation
- QoS for Microsoft Teams (Datacenter vGR + Branch z40)
- Tunnel Failover (z40 ↔ vGR) — WAN00 (wired) primary, WAN03 (4G) & WAN04 (5G) backups
- IP Routing & Static Route Steering (z40 Branch)
- VLAN & Layer-2 Bridging
-
-
-
-
-
-
- Articles coming soon
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
-
-
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
- Articles coming soon
-
-
- Articles coming soon
-
- IPsec Tunnel not Establishing
- SSL-VPN Tunnel not Establishing
- Mobile Network Issues
- Management Tunnel does not Establish
- DNS not Resolving from Local Network Appliance
- DNS Resolution Issues in Tunnel Configuration
- DHCP Server not Leasing IP to LAN PC
- Debugging EC Events - Unknown Status Issue
- Trusted-MAC Geofencing Issues
- DNS Issues from DC LAN PC
- Troubleshooting LAN Connectivity to Internet via WAN, Remote Branch LAN, or Local Branch LAN
- NetBalancer gateways displaying Faulty/Inactive
- Packet Drop Issues
-
-
zAccess
-
StorTrends
Bypass Rules
While SSL inspection is vital for detecting threats hidden in encrypted traffic, exceptions must be made for several common scenarions. These could be technical compatibilty issues, Legal and Regulatory Compliance, & Performance and reliability. So this configuration setting similar to a firewall rule, allows to add rules to bypass packets being inspected. The bypass can be performed based on IP, FQDN, Application, & Web Categories.
Additionally any apps defined as SAAS, can be bypassed by the flip of a switch. For example Microsoft strongly recommends bypassing SSL inspection (or SSL Bumping) for Microsoft Teams and other Microsoft 365 services to ensure optimal performance, reliability, and security. This can be done either from the Bypass Rules page or from Firewall->Advanced


Known Limitations:
- DNS Caching and Policy Enforcement Delay
- Previously resolved IP addresses for a domain or URL may continue to be used until the DNS cache expires or is refreshed.
- As a result, a domain or URL may remain accessible for a short period after a blocking policy is applied, or may remain blocked after being allowed.
- The updated policy will take effect only after the relevant cache entries are cleared or expire.